Expressvpn Glossary
Public key infrastructure (PKI)
What is public key infrastructure?
Public key infrastructure (PKI) is a framework that manages the creation, distribution, use, and validation of digital certificates and the cryptographic key pairs behind them. It provides a reliable way to verify identities and secure communication across networks.
How does public key infrastructure work?
PKI works by linking public keys to verified identities through certificates signed by trusted certificate authorities (CAs). The process starts when a user or system requests a certificate. A CA verifies the requester’s identity and, once satisfied, issues a digitally signed certificate that binds the public key to that identity. When another system, such as a browser, mail server, or virtual private network (VPN) client, receives this certificate, it validates the CA’s signature and trusts the public key.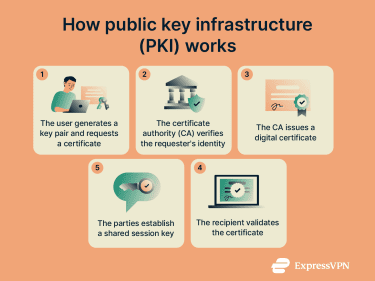
With that trust in place, the systems exchange encryption keys, typically by protecting a freshly generated session key with the verified public key. This exchange gives both sides a shared secret, allowing them to establish a secure communication channel.
Components of PKI
PKI relies on a set of coordinated components that issue, validate, store, and manage digital signatures, including:
- Certificate authority (CA): Verifies identities and issues signed digital certificates that establish trust in a PKI system.
- Registration authority (RA): Validates identity information for certificate requests and submits approved requests to the CA for issuance.
- Certificate database: Stores issued certificates and related metadata needed for certificate tracking and lifecycle management.
- Central directory: Provides a location where certificates and CA information can be retrieved so systems can perform validation.
- Certificate management system: Handles certificate enrollment, renewal, revocation, and auditing to maintain consistent certificate operations.
- Certificate policy (CP): Defines the rules and security requirements that govern how certificates are issued and used.
Types of public key infrastructure
- Hierarchical PKI: Uses a root CA that delegates trust to subordinate CAs, creating a structured chain where certificates are validated through the trust path.
- Mesh PKI (cross-verified PKI): Uses multiple CAs that establish trust by cross-certifying one another. It creates a network of direct trust links suited for distributed environments.
- Bridge CA architecture: Uses a bridge CA to connect separate PKI systems by providing cross-certification between them. This allows independent PKIs to trust each other without merging structures.
- Hybrid PKI: Combines elements of hierarchical, mesh, or bridge designs to support environments with mixed trust requirements or legacy systems.
Why is PKI important?
PKI matters because it creates a trustworthy environment for digital communication. It enables systems to confirm identities, protect data from interception, and detect tampering. This trust layer is essential for secure web traffic, authenticated devices and users, and the integrity of software and documents across networks that don’t inherently provide security.
It also helps organizations meet regulatory and policy requirements by providing auditable mechanisms for key management, certificate lifecycle management, and identity verification.
Security and privacy considerations
PKI security depends on the protection of private keys and the integrity of the CAs. If a CA is compromised or a private key is exposed, attackers may impersonate legitimate services or intercept encrypted communication. Strong physical, procedural, and technical controls are required to protect CA infrastructure and key material.
Certificate lifecycle management is equally important. Expired, misconfigured, or revoked certificates must be detected and removed from use. PKI itself protects the integrity and authenticity of communications, but logs, metadata, and operational records must also be secured to prevent leakage of sensitive usage information.
Further reading
- What is data encryption?
- Zero-trust data protection explained
- Internet infrastructure: What it is and how it works
