Expressvpn Glossary
Data transmission

What is data transmission?
Data transmission is the process of sending digital information between devices or systems. It enables communication across networks, both locally and over the internet.
Transmission can occur over wired connections such as Ethernet and fiber-optic cables, wireless connections such as Wi-Fi and cellular networks, or satellite links. Transmission performance is commonly measured by throughput, delay (latency), and reliability.
Communication protocols define how systems format, address, transmit, route, and sometimes verify data.
How does data transmission work?
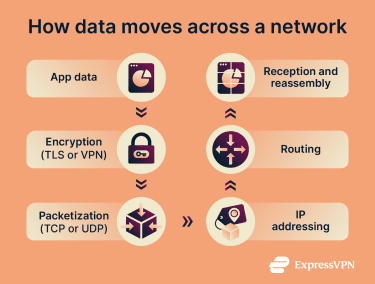
Data transmission converts information into signals, sends them across a connection, and reconstructs them at the destination. This process involves five key steps:
- Encoding: Devices encode data into signals, such as electrical signals over copper cables, radio waves for wireless, or light pulses for fiber-optic transmission.
- Packetization: Systems split data into smaller units, such as packets or frames, so networks can transmit and reassemble it efficiently. Depending on the protocol, these units may also carry addressing and sequencing information.
- Forwarding and routing: Network devices move data toward its destination. Switches usually forward frames within a local network, while routers forward packets between networks.
- Reassembly: The receiving device collects the transmitted units and reconstructs the original data in the correct order when required by the protocol.
- Integrity checks: Protocols may check whether the received data was corrupted in transit. Depending on the protocol and layer, errors may be detected with checksums, corrected, or handled through retransmission.
Types of data transmission
Data transmission is categorized by communication direction, delivery method, and transmission medium.
By direction
- Simplex: Communication flows in one direction only. One device sends data, and the other receives it (for example, a TV broadcast).
- Half-duplex: Both devices can send and receive data, but not at the same time. Communication alternates between directions (for example, walkie-talkies).
- Full-duplex: Devices send and receive data simultaneously (for example, a telephone call).
By delivery method
- Unicast: One sender transmits data to one specific recipient (for example, email or direct message).
- Multicast: One sender transmits data to multiple recipients that have joined a specific group (for example, some enterprise video streams or conferencing systems).
- Broadcast: One sender transmits data to all devices within a network segment (for example, local network announcements).
By transmission medium
- Wired: Data flows through physical cables, such as Ethernet over copper or fiber-optic lines.
- Wireless: Data travels without physical cables using radio frequencies or infrared light (for example, Wi-Fi, Bluetooth, cellular networks, and satellite links).
Why is data transmission important?
Billions of people depend on data transmission for mobile connectivity and digital communications. Broadband, Wi-Fi, and cellular networks enable everyday activities like browsing, streaming, messaging, and online gaming.
Remote workers rely on data transmission for video conferencing, file sharing, and access to collaboration platforms. These activities depend on networks that can move data reliably between users and online services
Beyond personal and office use, data transmission powers many automated systems. Internet of Things (IoT) devices, healthcare monitors, and industrial systems depend on timely data transmission to function. These systems exchange sensor data, commands, and status updates in real time.
It's also critical for financial infrastructure. For example, an online purchase typically involves data moving between the customer, merchant, payment processor, or network intermediaries, and the bank, along with related business systems.
Risks and privacy concerns
Data transmission can expose sensitive information if it's not properly protected. An attacker or unauthorized party with access to the network path can capture unencrypted data. Common methods include packet sniffing and man-in-the-middle (MitM) attacks. MITM attacks also allow attackers to alter data in transit.
Even with encryption, some transmission metadata may remain visible. Source and destination addresses, connection timing, and data volume can reveal communication patterns that may expose user behavior and relationships.
Further reading
- How does the internet work?
- What are network protocols?
- What is a network connection?
- Throughput vs. bandwidth: What’s the difference?
- What is network jitter?

