Expressvpn Glossary
Network forensics
What is network forensics?
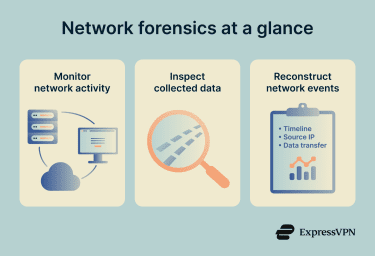
Network forensics is the process of collecting and examining network traffic data to investigate security incidents. It looks at how devices communicate across a network and uses that information to understand what happened during a suspected breach or misuse of systems.
The focus is on network activity, such as data packets, flow records, and system logs, rather than files stored on individual computers. The goal is to reconstruct events, confirm whether unauthorized activity occurred, and determine which systems or data were involved.
How does network forensics work?
Network forensics is a branch of digital forensics that relies on recorded network data.
The process usually follows these steps:
- Identification: The investigation begins by defining the scope, including identifying the affected systems, the suspected timeframe, and the type of incident. A clear scope determines what data needs to be collected and which tools to use.
- Preservation: Relevant evidence is secured to prevent tampering or accidental damage. Copies of network data and logs are created and stored safely. Integrity controls such as cryptographic hashing and chain-of-custody records may be used if legal review is possible.
- Collection: Investigators gather network data such as packet captures, flow records, and device logs. The data can be collected manually, automatically, or using a combination of both.
- Examination and analysis: The collected data is reviewed to identify unusual patterns, suspicious connections, and indicators of compromise. Traffic data, metadata, and system logs are correlated to determine how the incident occurred and what systems were affected.
- Reporting: Findings are documented in a clear, factual report that outlines the evidence, timeline of events, and impact of the incident. It may support incident response actions, compliance requirements, or legal proceedings.
Why is network forensics important?
Network forensics provides visibility into network activity. It helps organizations:
- Confirm whether a breach happened.
- Understand the scope of the incident and verify what data left the network.
- Respond to and contain incidents more effectively.
- Improve the accuracy of incident reporting.
- Strengthen future security controls.
- Meet regulatory and legal reporting requirements.
Where is network forensics used?
Network forensics is often used in:
- Incident response: Traffic logs are reviewed to identify the source and timeline of an attack.
- Data breach investigations: Analysis determines whether confidential information left the network and how it was accessed.
- Malware analysis: Outbound connections may reveal communication between infected systems and external control servers.
- Insider threat investigations: Unusual internal traffic can indicate misuse of authorized access.
- Distributed denial-of-service (DDoS) analysis: Traffic volumes and patterns are examined to identify attack sources and affected sources and inform mitigation strategies.
Risks and privacy concerns of network forensics
Because network forensics involves collecting network activity data, it may include sensitive or personal information. Key risks involve:
- Exposure of confidential information within captured traffic.
- Monitoring beyond what is necessary for security purposes.
- Non-compliance with data protection laws (if the collection is excessive or if the data is collected improperly).
- Unauthorized access to stored forensic data.
Further reading
- How to prevent packet sniffing attacks
- Deep packet inspection (DPI): How it works and why it matters
- What is cyber threat hunting, and how does it work?
- Reconnaissance in cybersecurity: Everything you need to know
- What is unified threat management (UTM)?
FAQ
What’s the difference between network forensics and digital forensics?
What types of data are used?
Can encrypted traffic still be investigated?
Another option is to provide the investigator with decryption keys. In that case, they can fully decrypt and inspect the traffic.

